Digital certificates are equivalent to a website’s identification card, or driver’s license, ensuring that a website is real and not a scam website attempting to steal users’ personal information, such as credit card numbers. Trusted certificate authorities (CAs) are entities that issue these certificates, which can be used in HTTPS, the secure browsing protocol for the World Wide Web, or as identity cards for national governments for use in electronically signing documents.[1] Certificates are digital documents that provide a person, company, or any other entity a trusted method of sharing their identity. Clients use CA certificates to authenticate the CA signature on the server certificate, as part of the authorizations before launching a secure connection.[1] For instance, when connecting to Amazon’s website, the company’s server sends Amazon’s certificate to each user. The certificate verifies an identity and enables private communication.
At SHARE Fort Worth, Broadcom software engineers Seamus Hayes and Jamieson Walker explained that digital certificates also contain a cryptographic key that can be used to send encrypted messages to the server, allowing for private, secure communication. They shared, “In the last 10 years, technologies such as transport layer security have greatly reduced the risk of shopping, banking, and existing on the World Wide Web.”
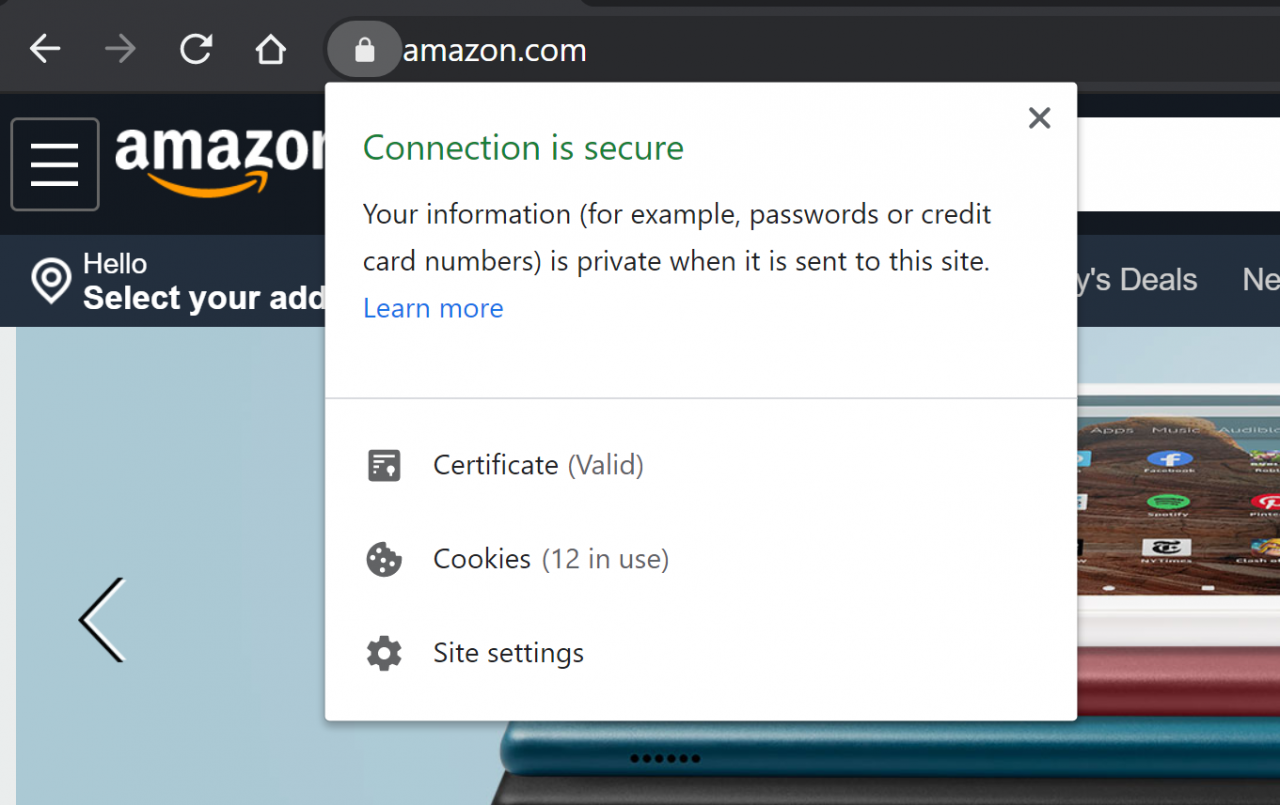
Example: When you hover over the “lock” icon in a browser, it shows the server’s certificate information.
Digital certificates have become the backbone of a secure and private internet, which has led to increased safety online. The technology protects customer and business data at the “heart of every organization,” noted Hayes and Walker. “Customers today expect that their data is secure every step of the way. Customer-facing websites, internal authentication services, network traffic, and more should be verified and secured. And, implementing a good digital certificate infrastructure is essential to protecting your customers.”
Because mainframes run 30 billion transactions per day and house 80% of the world’s business data, this data must be secured while stored, sent, and received, and it must be transferred only between valid sources. Hayes and Walker explained that digital certificates provide a strong, mathematically-proven way to accomplish these tasks. Programmers can leverage a mainframe’s external security managers (ESMs) to create certificates, as well as manage them and protect business and consumer data so it is not compromised when leaving the system. “By identifying your systems and services with digital certificates, you can securely and seamlessly integrate mainframes and new distributed systems into your IT infrastructure,” they said.
“For the system administrators preparing to set up certificates on your site, we offer you some words of wisdom,” said Hayes and Walker. “Find comfort in the knowledge that implementing certificates is confusing no matter who you are. Any sufficiently-complex network topology, with all the incoming and outgoing connections, will be difficult to administer.” They added that you need to understand digital certificates, why they are needed, and how they work before implementing certificates on a website. “Many times customers will ask questions like, ‘Why does this particular certificate for server A need to be loaded into a keyring for server B?’ When given an understanding of how certificates are used, they can answer the question for themselves,” Hayes and Walker detailed.
Debugging Tips
Both said that debugging digital certificate issues can be a long and tedious process. They advise using ESM commands that can be run to examine information about certificates and their private keys to ensure that they are valid and complete. “ESM security violations can be examined to warrant that users are permitted access to the certificates they need to do their job,” they explained. “Vendor support is also available from IBM and Broadcom for ESM setup and management of certificates; your company's trusted CA can be an invaluable resource when troubleshooting issues inside a certificate.” The best way to alleviate complications, they said, is to better understand digital certificates.
“If you are struggling to get the proper keys setup with the right extensions and parameters, read up on TLS and digital certificate PKI research and articles. The more you understand about the subject, the better equipped you will be to diagnose and solve a problem,” advised Hayes and Walker. “If you are having trouble storing, protecting, and retrieving certificates, read up on your ESM. Browse public support cases about certificate setups and management issues.” They noted that practicing the ESM commands and setups on a test system and becoming familiar with the description and functionality of keyrings and certificate owners is an essential part of the process. “Each use case is different and you know your company's situation best,” they added. “When all else fails, reach out for support.”
Digital certificates, however, do require up-to-date information to ensure private keys are safe and uncompromised. Many of these keys have built-in expiration dates that must be managed to ensure digital certificates are secure. Leveraging digital certificates properly will keep your customer and business data safe as you move it around networks, around the world. As security remains a top concern of businesses today, digital certificates are one way to ensure your business’ websites are considered trusted sources.
The ‘DOs’ of Digital Certificates
- Understand how and why digital certificates work to provide private and secure communication
- Spend the time and money to get certificates signed by a trusted and reputable CA
- Develop and strictly follow certificate rotation and replacement policies
- Restrict access to digital certificates, especially their private keys via an ESM
- Stay up-to-date on digital certificate research and news (it is important to use large enough public and private keys and key algorithms, and to phase out keys as they become obsolete)
The ‘DON’Ts’ of Digital Certificates
- Use a single certificate for every server/connection in your domain
- Use self-signed certificates to secure customer-facing websites/APIs, or as a permanent solution for internal connections
- Carelessly share your private key; this includes transferring/copying it between your systems (any exposure of the private key risks compromising your security)
[1] https://en.wikipedia.org/wiki/Certificate_authority